Chapter 5: Selection & Interfaces
Core product introduction, typical wiring diagrams, interface logic, and product function comparison tables
Selecting the right products for a network identity authentication system requires evaluating performance, scalability, integration capabilities, and vendor support. This chapter introduces the six core product categories, presents their typical wiring and interface logic, and provides comprehensive function comparison tables to guide procurement decisions. Each product category is evaluated against a standardized set of criteria relevant to enterprise identity authentication deployments.
5.1 Core Product Introduction
The six core product categories form the foundation of every enterprise identity authentication system. Each category serves a distinct function in the authentication chain, from directory services and certificate issuance to network enforcement and audit logging. The following product showcase illustrates representative appliances from each category, with key specifications and deployment roles.

Figure 5.1: Core Product Showcase — Six product categories: RADIUS/AAA Server (1U rack), Network Access Control appliance (2U rack), PKI/CA Server (rack), Enterprise Access Switch (802.1X capable), Wireless Controller (1U), and PAM Jump Server (rack)
| Product Category | Primary Function | Key Protocols | Form Factor | HA Model |
|---|
| RADIUS/AAA Server | Authentication, Authorization, Accounting | RADIUS (UDP 1812/1813), EAP, CoA (UDP 3799) | 1U rack appliance or VM | Active-Active cluster |
| Network Access Control (NAC) | Device profiling, posture assessment, policy enforcement | SNMP, DHCP, HTTP, REST API | 2U rack appliance or VM | Active-Standby |
| PKI/CA Server | Certificate issuance, revocation, OCSP | SCEP, EST, OCSP, CRL (HTTP/HTTPS) | Rack appliance + HSM | Sub-CA clustered; offline root |
| Enterprise Access Switch | 802.1X authenticator, VLAN enforcement, PoE | 802.1X, RADIUS, SNMP, SSH, NETCONF | 1U/2U rack switch | Stacking or VSS |
| Wireless Controller | SSID management, EAP proxy, VLAN assignment | CAPWAP, RADIUS, 802.1X, SNMP | 1U rack appliance or cloud | Active-Standby or N+1 |
| PAM Jump Server | Privileged session brokering, credential vault, recording | SSH, RDP, HTTPS, TACACS+, LDAP | 2U rack appliance or VM | Active-Standby |
5.2 Typical Wiring and Interface Logic
The interface logic diagram illustrates the physical port layout of the RADIUS/AAA server and its logical connections to all integrated systems. Understanding the interface mapping is essential for firewall rule creation, network segmentation, and troubleshooting. Each interface serves a specific function, and mixing authentication traffic with management traffic on the same interface is a security anti-pattern that must be avoided.
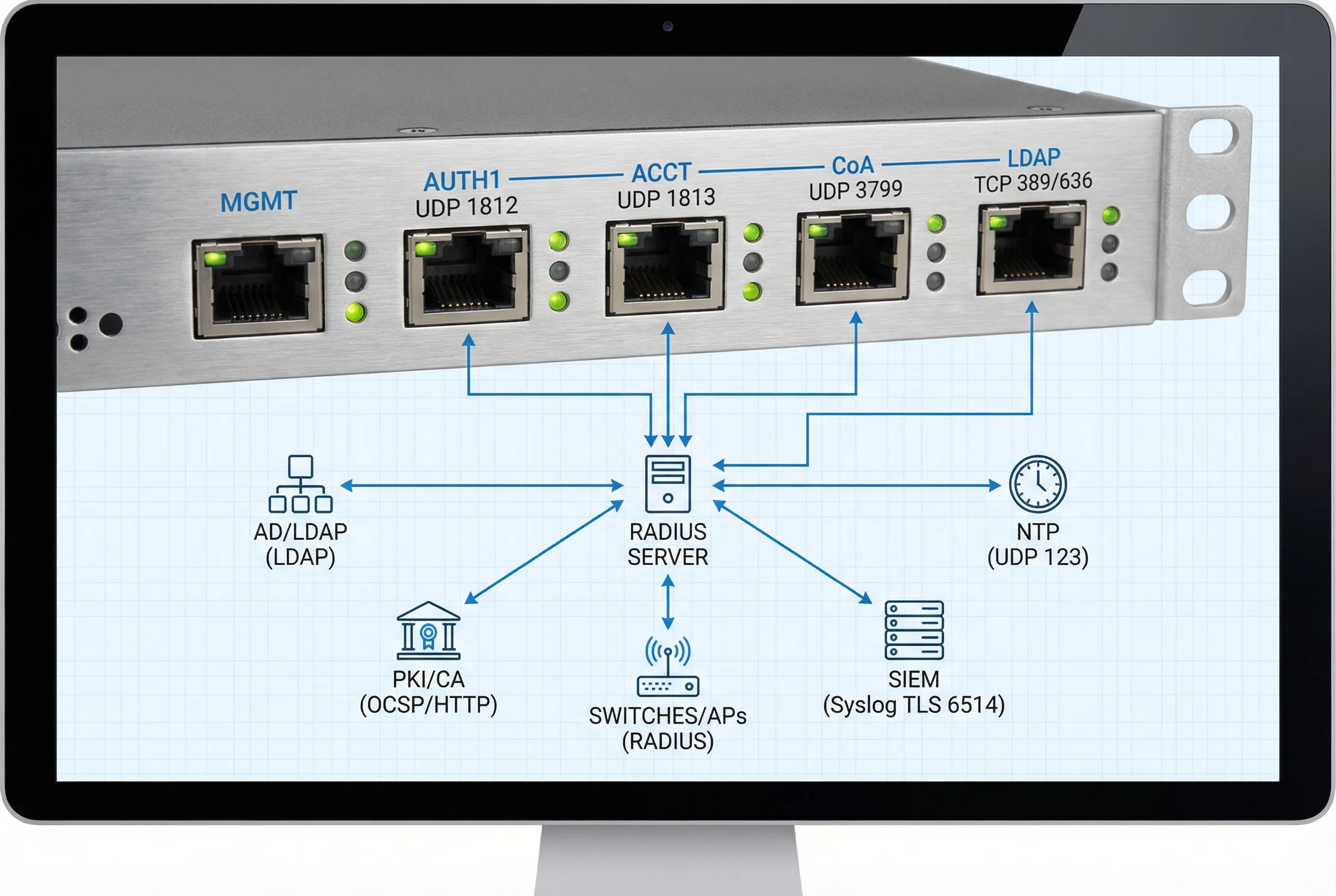
Figure 5.2: RADIUS Server Interface and Connection Logic — Front panel ports (MGMT, AUTH1 UDP 1812, ACCT UDP 1813, CoA UDP 3799, LDAP TCP 389/636) with logical connections to AD/LDAP, PKI/CA (OCSP), Switches/APs (RADIUS), SIEM (Syslog TLS 6514), and NTP (UDP 123)
| Interface | Protocol | Port | Direction | Connected System | Security Requirement |
|---|
| MGMT | SSH, HTTPS | 22, 443 | Inbound | PAM Jump Server only | MFA required; IP whitelist enforced |
| AUTH1 | RADIUS | UDP 1812 | Inbound | Switches, WLC, VPN | RADIUS shared secret ≥ 32 chars; IP whitelist |
| ACCT | RADIUS Accounting | UDP 1813 | Inbound | Switches, WLC, VPN | Same shared secret as AUTH1 |
| CoA | RADIUS CoA | UDP 3799 | Outbound | Switches, WLC | Separate shared secret; IP whitelist on switch |
| LDAP | LDAPS | TCP 636 | Outbound | AD/LDAP Server | TLS required; certificate validation enforced |
| OCSP | HTTP | TCP 80 | Outbound | PKI/CA OCSP Responder | Internal CA only; no internet OCSP |
| Syslog | Syslog/TLS | TCP 6514 | Outbound | SIEM | TLS mutual auth; CEF format |
| NTP | NTP | UDP 123 | Outbound | Internal NTP Server | NTP authentication (MD5/SHA1) |
5.3 Core Product Function Comparison
The following tables provide detailed function comparisons across the key product categories. These comparisons are designed to support procurement decisions by highlighting the functional differences between product tiers and vendors. Organizations should evaluate products against their specific scenario requirements identified in Chapter 3, using these tables as a structured scoring framework.
5.3.1 RADIUS/AAA Server Feature Matrix
| Feature | Basic Tier | Standard Tier | Enterprise Tier | Requirement Level |
|---|
| EAP-TLS support | Yes | Yes | Yes | Mandatory |
| EAP-TTLS / PEAP | Yes | Yes | Yes | Recommended (BYOD) |
| LDAP/AD integration | Basic LDAP | LDAP + AD groups | Full AD + SAML + OIDC | Mandatory |
| Dynamic VLAN assignment | Yes | Yes | Yes + policy engine | Mandatory |
| CoA (RFC 5176) | Limited | Yes | Yes + automation | Mandatory |
| OCSP/CRL integration | CRL only | OCSP + CRL | OCSP stapling + CRL | Mandatory (OCSP) |
| Auth throughput | 500 auth/s | 2,000 auth/s | 10,000+ auth/s | Size to peak × 1.3 |
| Clustering | No | Active-Standby | Active-Active N+1 | Mandatory (Active-Active) |
| REST API | No | Read-only | Full CRUD + webhooks | Recommended |
| SIEM integration | Syslog UDP | Syslog TLS | Syslog TLS + CEF + API | Mandatory (TLS) |
5.3.2 NAC Platform Feature Matrix
| Feature | Basic Tier | Standard Tier | Enterprise Tier | Requirement Level |
|---|
| DHCP fingerprinting | Yes | Yes | Yes + ML profiling | Mandatory |
| SNMP OID profiling | Limited | Yes | Yes + custom OID | Recommended |
| HTTP user-agent profiling | No | Yes | Yes + passive TLS | Recommended |
| MDM/EDR integration | No | API (1–2 vendors) | API (multi-vendor) | Mandatory for BYOD |
| Captive portal | Basic | Customizable | Full branding + sponsor | Mandatory (guest) |
| Posture assessment | No | Basic (OS, AV) | Full (OS, AV, patch, EDR) | Recommended |
| CoA enforcement | Yes | Yes | Yes + automation | Mandatory |
| Concurrent sessions | 5,000 | 25,000 | 100,000+ | Size to peak × 1.3 |
5.3.3 PAM Platform Feature Matrix
| Feature | Basic Tier | Standard Tier | Enterprise Tier | Requirement Level |
|---|
| SSH session brokering | Yes | Yes | Yes + protocol isolation | Mandatory |
| RDP session brokering | No | Yes | Yes + protocol isolation | Recommended |
| Credential vault | Basic | Yes + rotation | Yes + HSM + rotation | Mandatory |
| Session recording | Text log only | Video + text | Video + text + OCR search | Mandatory (video) |
| MFA enforcement | TOTP only | TOTP + push | FIDO2 + TOTP + push | Mandatory |
| TACACS+ integration | No | Yes | Yes + command-level | Mandatory |
| Break-glass workflow | Manual | Automated + approval | Automated + approval + review | Mandatory |
| SIEM integration | Syslog | Syslog TLS + CEF | Syslog TLS + CEF + API | Mandatory (TLS) |