Network Identity Authentication
Architecture Design Guide
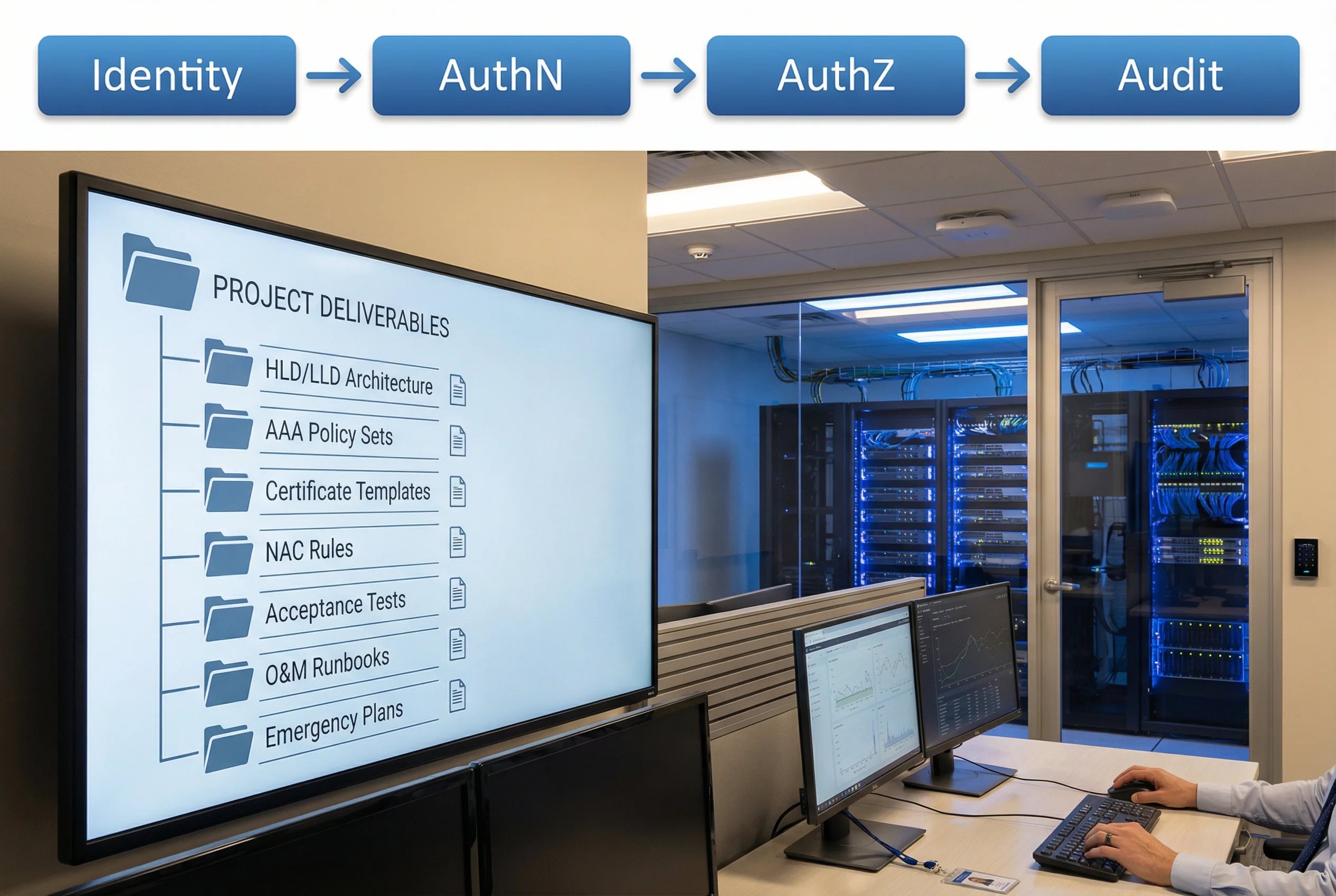
An engineering-grade reference for designing, deploying, and operating a unified network identity authentication system — covering AAA, 802.1X, NAC, PKI, MFA, PAM, ZTNA, and end-to-end audit across multi-site enterprise environments.
System Overview
This guide defines an engineering-grade Network Identity Authentication System whose core goal is to form a closed loop of Unified Identity Source + Strong Authentication + Least-Privilege Authorization + End-to-End Auditing. The system unifies identity lifecycle for people, devices, and service accounts, and enforces access decisions consistently across wired, wireless, VPN/ZTNA, management access, and application entry points.
It is designed for procurement, implementation, delivery, and long-term operations, emphasizing interoperability with AAA (RADIUS/TACACS+), NAC, PKI, MFA/conditional access, PAM, SIEM, and NTP time synchronization. The architecture supports organizations with 2,000–10,000 users across 8–30 sites in mixed on-premises and cloud environments.
System Architecture
The reference architecture uses a single authoritative identity plane and multiple policy enforcement planes. The directory/IdP provides identity truth; AAA/NAC enforces access at network edges; PAM and TACACS+ control privileged operations; SIEM provides audit centralization. The four-layer model ensures clear separation of concerns and supports independent scaling of each tier.
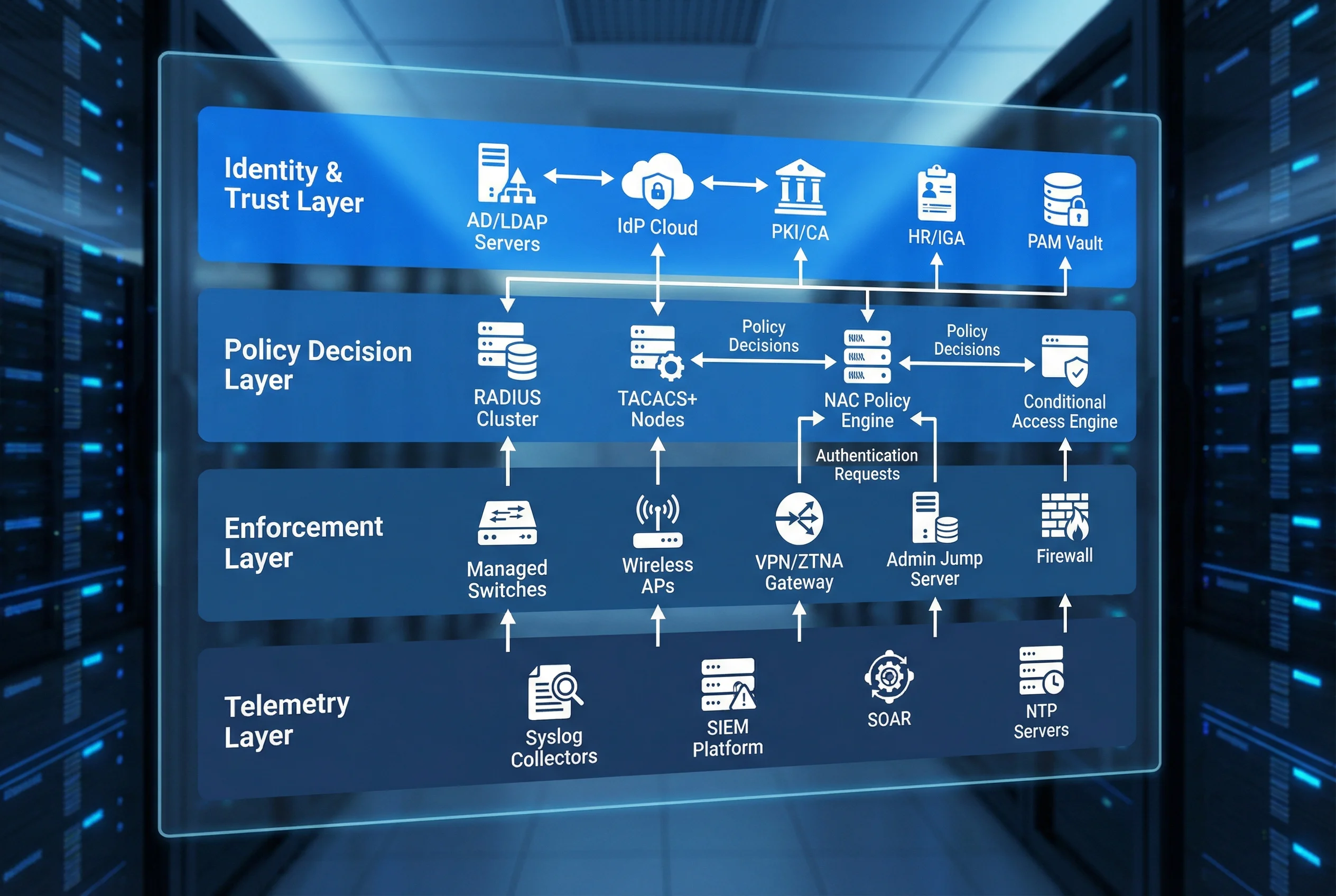
| Layer | Key Components | Primary Function | Key Protocols |
|---|---|---|---|
| Identity & Trust | AD/LDAP, IdP, PKI/CA, PAM, HR/IGA | Authoritative identity source and certificate trust | LDAP, Kerberos, SAML/OIDC, SCEP/EST |
| Policy Decision | RADIUS, TACACS+, NAC Engine, Conditional Access | Evaluate authentication and authorization requests | RADIUS (UDP 1812/1813), TACACS+ (TCP 49) |
| Enforcement | Switches, APs/WLC, ZTNA/VPN, Jump Server, Firewall | Apply access decisions at network edge | 802.1X/EAPOL, EAP-TLS, IPsec/TLS |
| Telemetry | Syslog/CEF, SIEM, SOAR, NTP, NetFlow | Centralized audit, correlation, and alerting | Syslog TLS (6514), NTP (UDP 123) |
Main Functions
The system delivers six integrated capability domains, each contributing to the overall security posture. The honeycomb model below illustrates how all six domains radiate from a central unified identity source, ensuring coherent policy enforcement across every access pathway.

| Function Domain | Value Delivered | Key Implementation | Acceptance Criterion |
|---|---|---|---|
| Unified Identity Lifecycle | Eliminates orphan accounts and inconsistent privileges | HR-driven provisioning, joiner/mover/leaver; MDM device enrollment; service account vault | Account disable/revoke within defined SLA; group mapping consistent |
| Strong AuthN — 802.1X EAP-TLS | Passwordless device identity; resists phishing | Certificate issuance, CRL/OCSP, supplicant config, fallback/MAB for legacy | Correct cert chain validation, dynamic VLAN/ACL, fail-closed for sensitive zones |
| Centralized AAA — TACACS+ | Command-level least privilege; full accountability | Per-role command sets, device privilege levels, unique admin IDs | Command logs correlate to user; deny unauthorized commands |
| NAC Profiling & Guest/IoT Onboarding | Contain unmanaged endpoints; reduce lateral movement | Device fingerprinting, DHCP/SNMP/RADIUS attributes, captive portal for guests | Correct segmentation for IoT/guest; posture-based quarantine works |
| Remote Access — MFA + ZTNA | Reduce risky logins; adapt to context | Risk score, device compliance, geo/IP reputation, step-up auth | High-risk blocked/step-up; policy exceptions documented |
| End-to-End Audit & Alert Linkage | Forensics-ready; faster incident response | Standardized log schema, correlation IDs, NTP, SIEM dashboards | "who/when/how/what" trace within minutes; alerting tested |
Scope & Key Dependencies
| Category | In-Scope |
|---|---|
| Identity | Central identity source (AD/LDAP/IdP), account lifecycle, group/role model |
| Network Access | AAA services, 802.1X EAP-TLS for wired/wireless, dynamic authorization (VLAN/ACL/SGT) |
| NAC | Profiling, posture/health checks, IoT/guest tiered onboarding |
| Remote Access | MFA, conditional access, risk-based policies (Zero Trust / ZTNA) |
| Privileged Access | PAM, session recording, command authorization, break-glass |
| Audit | Logging, correlation IDs, SIEM integration, time synchronization, alerting |